Fotolia
Microsoft Teams 101: A how-to guide for beginners
Are you just beginning to learn how to use Microsoft Teams? Here is a quick-start guide to help you navigate some common trouble spots with this collaboration tool.
Once considered the mainstay of far-flung IT teams and multinational business giants, remote work is now a common occurrence for businesses everywhere. While there are a number of platforms available to support remote collaboration, Microsoft Teams is one of the most popular tools available.
Teams operates like the "closed" network of an organization, where different "teams" can work on different "projects" in real time. Business teams can conduct meetings, edit Microsoft Office documents, connect to OneDrive for storage and sharing and use IM-like chat services to communicate.
To get started using Microsoft Teams, log in using your Microsoft 365 business or educational credentials to set up the full version. There is also a free version that only requires a Microsoft email address, but it does come with slightly limited functionality.
The following sections will cover most of what you will need to get started with Microsoft Teams.
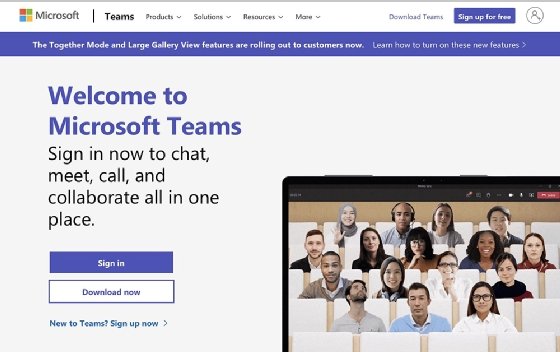
How to install Microsoft Teams
To install Microsoft Teams, follow these steps:
- Visit the official Microsoft Teams website to download the installer.
- Once you have downloaded and run the installer, enter your Microsoft email account and select Next. If you don't have one, you can create it by clicking the Create one! button.
- Then, enter your phone number and verify it.
- That's it. Teams should now be installed and ready to use on your device.
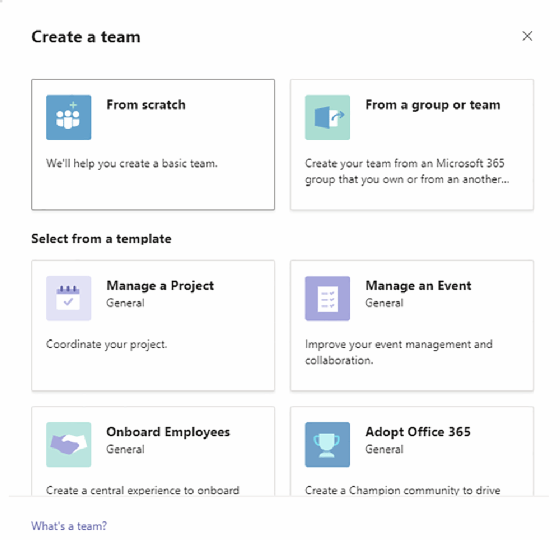
How to create a team and invite team members
To make a team and invite members to it, follow these steps:
- Select Teams from the tab on the left.
- Then select Create team.
- Choose Build a team from scratch.
- If you want everyone in the organization to have access to the team, select To restrict access, go with Private.
- Enter a name and description for your team, then select
- Next, add all the names of your team members to the list and click
- To add someone from outside the organization, you will have to send an invitation. Click the Invite People button on the bottom left to do so.
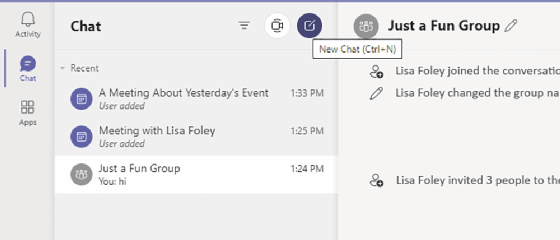
How to chat in Teams
To start chats in teams, follow these steps:
- Select Chat from the left.
- Then click the New Chat
![Window to start a new chat within Microsoft Teams]()
This menu within Team will enable you to start a new chat. - Enter the name of the person, type your message and hit send.
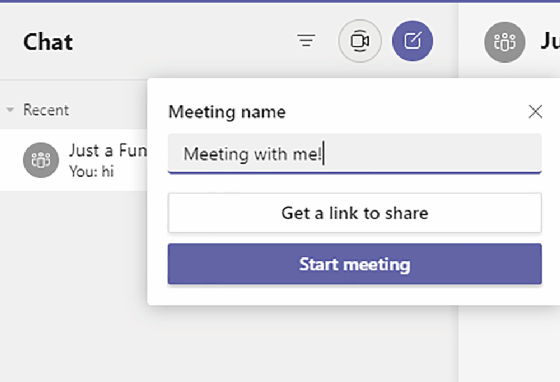
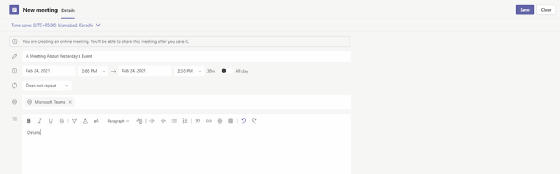
How to set/schedule meetings in Microsoft Teams
To set up and start a meeting right away, follow these steps:
- Click the camera icon at the top left of the app.
- Click Get a link to share and share the link with attendees. You can also just start the meeting and add attendees to it.
Alternatively, to schedule a meeting in Teams for a later time and/or date:
- From the panel on the left, select Apps > Calendar.
- Then, select New meeting.
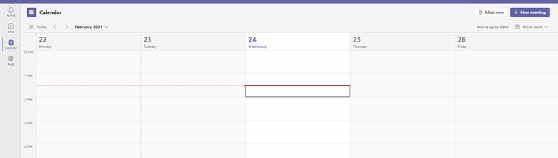
- Fill out the name, time, location and description for the meeting, then select Save. This will create the meeting on both the Teams and Outlook calendars.
- Choose from the pop-up menu whether you want to get a shareable link to the meeting or want to link it with Google Calendar.
How to share files in Teams
For file sharing in Teams, follow these steps:
- From within any conversation, click the paper clip
![File sharing within Microsoft Teams screenshot]()
- Browse to the file, upload it, and once done, hit Send.
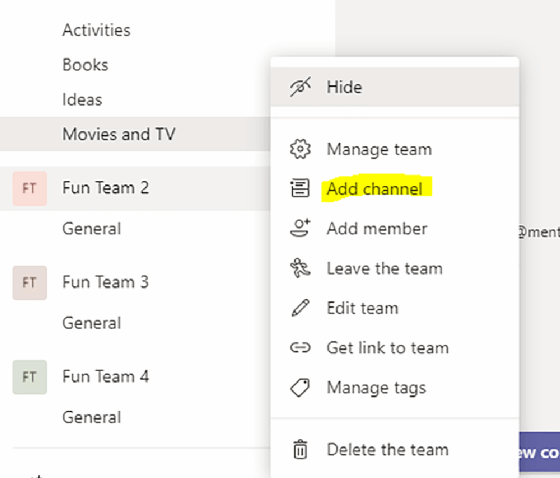
How to create channels within teams
If you have multiple projects to track, you can avoid unnecessary confusion by creating multiple Teams "channels." Here's how:
- Find the team that would you like to create a channel within, then select More options > Add channel.
- Enter the name and description for the new channel. By default, the privacy setting is set to Standard -- Accessible to everyone on the team. If you wish to create a private channel, just change it to Private -- Accessible only to a specific group of people within a team.
- Click Add once done.
How to use Teams for voice and video calls
To make a voice or video call in Teams:
- While on any channel team, or chat, click the camera or phone icon to start a voice or video call.

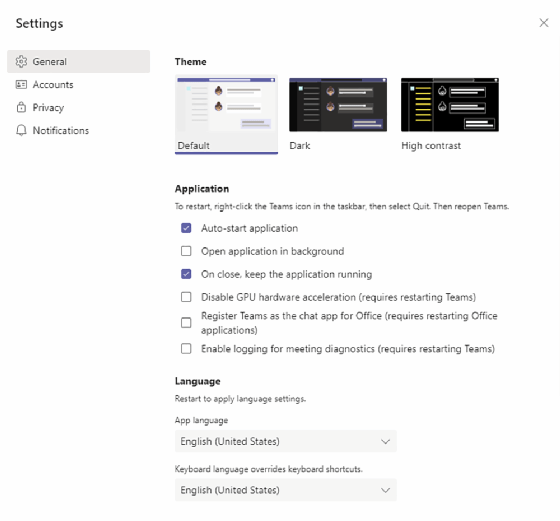
How to change the Teams display theme
You can also change the display theme for Microsoft Teams, which will alter your overall aesthetic experience of the application. There are three available options: Default, which combines violet and grey color coding; Dark, which replaces the grey with black; and High contrast, which uses strongly contrasting colors to make text easier to read. Here's how:
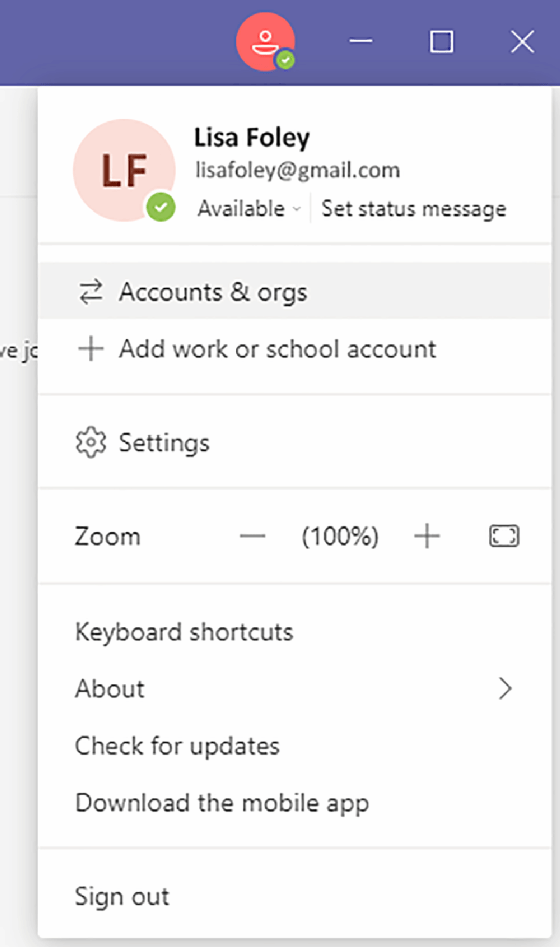
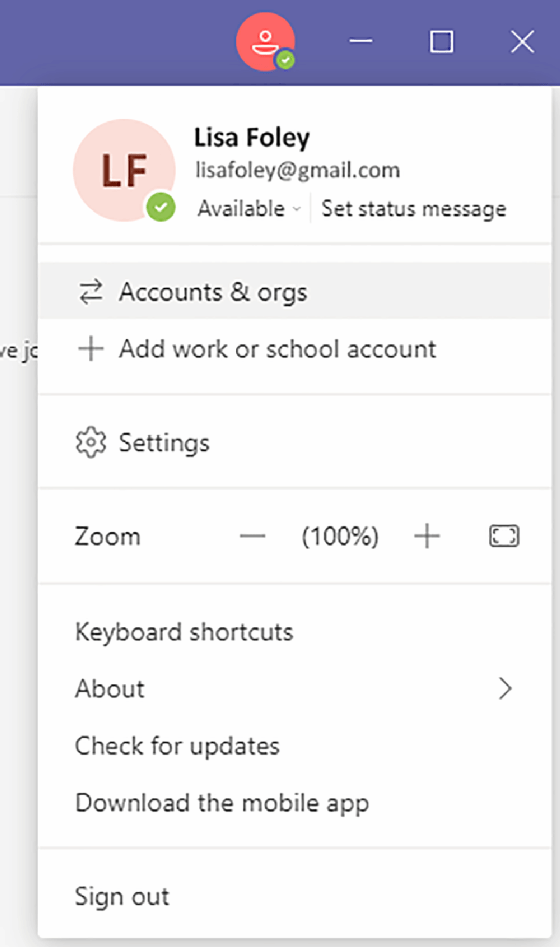
- Click the profile icon right next to the minimize button. Then select
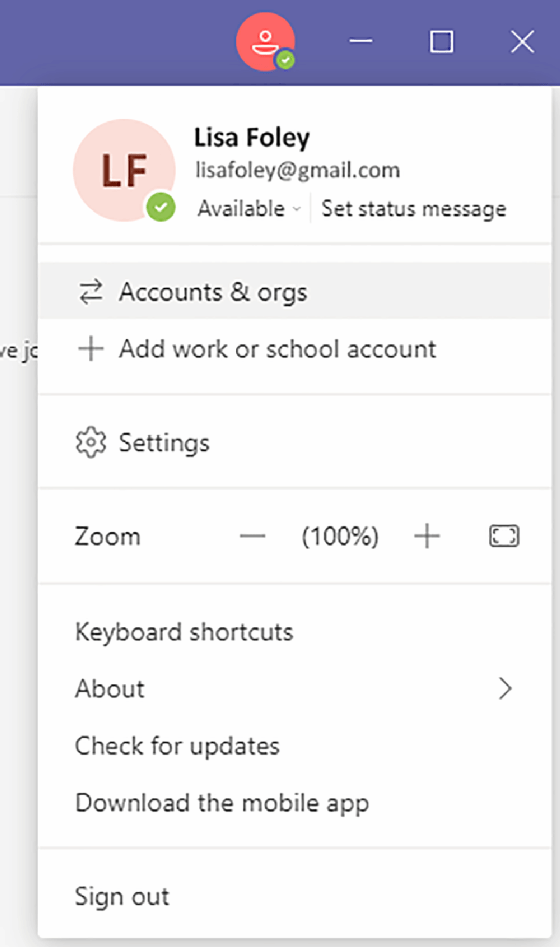
- Click on the desired theme at the top to switch.
Recording audio/video calls
To record an audio or video call in Teams:
- While in the meeting, go to meeting controls and then choose More options > Start recording. Everyone in the meeting will be notified that the recording has begun.
- To stop recording, once again go to the meeting controls and then select More options > Stop recording.
While recording audio and video calls in Teams is an option, it is important to note that some states require two-party consent to initiate a recording. This means that all parties involved in the call must agree to being recorded.
Learn more here about which states require two-party consent. Also, read some advice from experts in the field about video conferencing privacy.
How to delete video recordings and messages in Teams
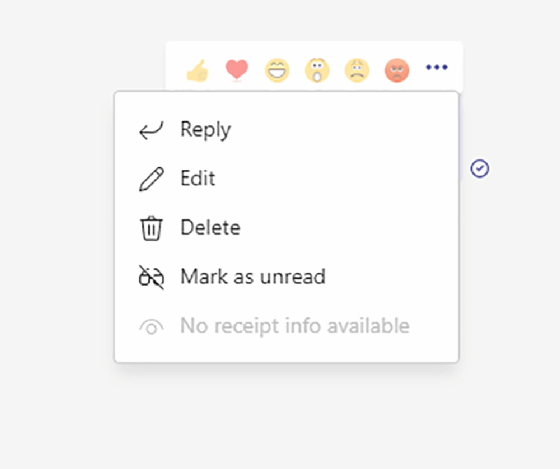
To delete a message in Teams:
- Hover over the message. Then select More options > Delete.
Teams meeting recordings can either be saved in OneDrive or SharePoint. To delete them, you will have to log in to your OneDrive or SharePoint account.
How to leave a group chat in Teams
To leave a group chat in teams, follow these steps:
- Click the Chat icon on the left to open all of your chats.
- Navigate to the group you want to leave. Then, click More options > Leave.
How to integrate Teams with other apps
To add even more functionality to Teams, you can integrate it with other apps. Here's how:
- Select Apps from the left-hand bar.
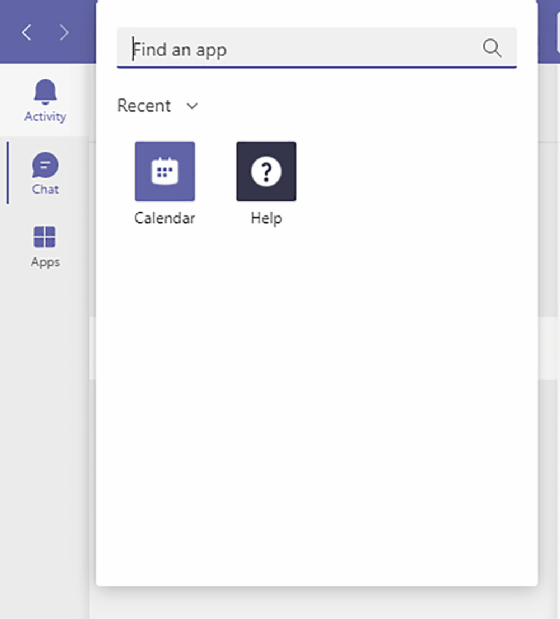
- Search for the relevant app, select it and then add it. Apps that you can choose from include Google Analytics, HubSpot, Microsoft Dynamics 365, Salesforce, Trello, Zendesk and more.
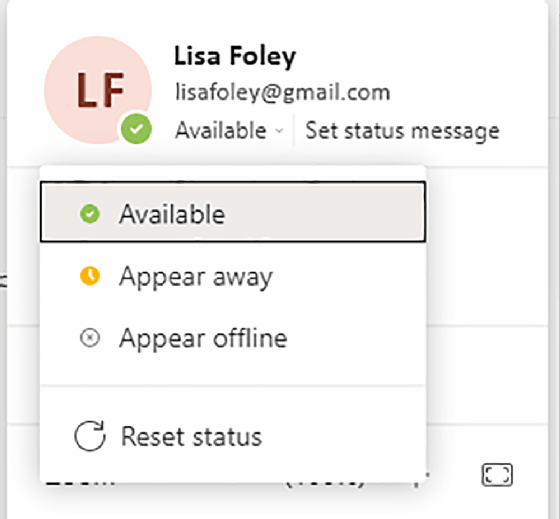
How to appear offline or away in Teams
If you wish to appear offline or away in Teams:
- Click the profile icon right next to the minimize button.
- Then, click on the current status, and select whether you want to appear away or offline.
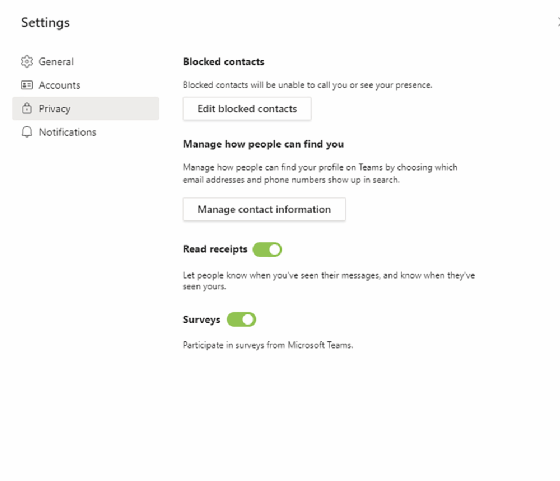
How to turn read receipts off in Teams
To turn read receipts off, follow these steps:
- Click the profile icon right next to the minimize button. Then select
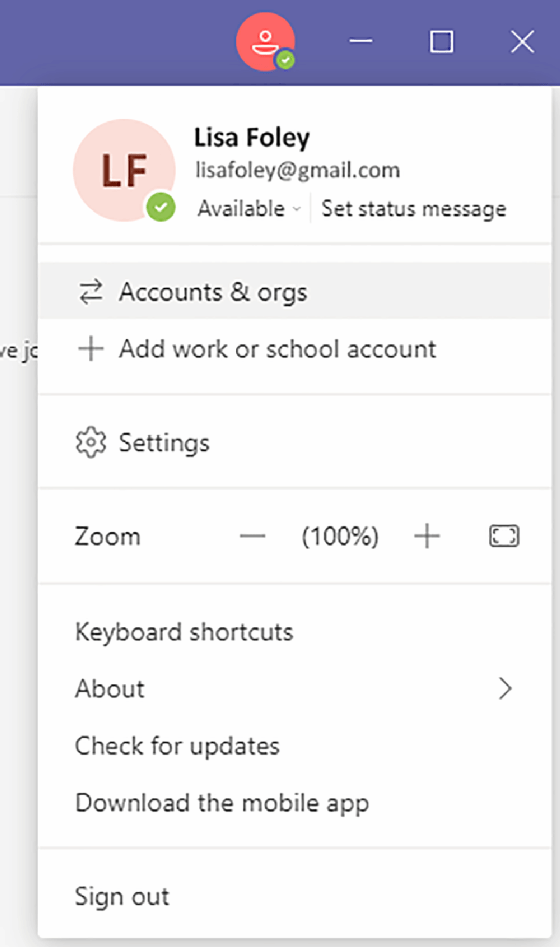
- Move over to the Privacy
- Then toggle the Read receipts button to off.
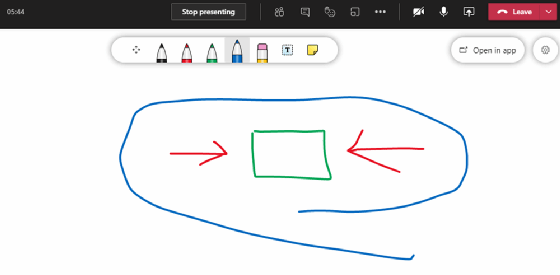
How to collaborate on a whiteboard in Microsoft Teams
During meetings on Microsoft Teams, attendees can collaborate on a whiteboard -- a shared, freeform digital canvas on which meeting participants can write and draw -- much like a traditional whiteboard in a physical conference room. Here's how:
- While in a meeting, select the Share
- From the Whiteboard section, click Microsoft Whiteboard.
- You can ink or type on the canvas that appears. To add text, select the Note or Text
- To add ink, select the Pen icon, which can be used to draw, sketch or even type.
How to add an account to Teams
You can add more than one account to Microsoft Teams. Here's how:
- Click the profile icon right next to the minimize button. Then select
- Move over to the Accounts
- Under Add account, press
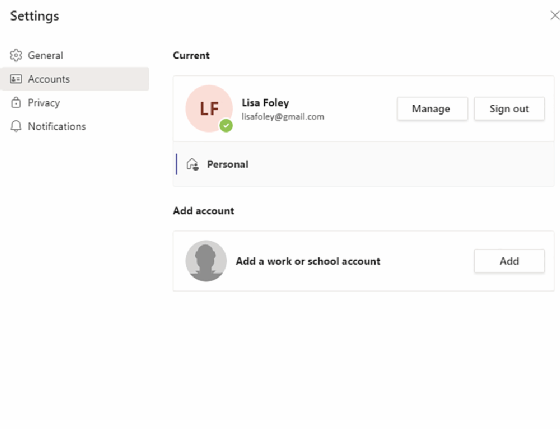
- Follow the on-screen instructions to add the account.
Microsoft Teams privacy and security features
Encrypted video and audio, industry standard protection against cyberattacks, and stringent privacy policies to protect user identity make Microsoft Teams a highly secure platform. This is certified by compliance with more than 90 regulatory and industry standards for data security and user privacy.
Teams runs on the same security framework as Microsoft's 365 cloud infrastructure. The Office 365 Advanced Threat Protection technology scans attachments and files uploaded to Teams to identify malware. The platform employs single sign-on, two-factor authentication and data encryption to protect against unauthorized access. Teams also supports auditing and reporting, legal hold, retention policies, and e-discovery.
Additional tips and tricks
Here are a few more Teams tips and tricks that may come in handy:
- If you have used Microsoft Outlook or Microsoft Word at all, most of the controls -- particularly for formatting text -- are identical.
- You can mark a message as urgent to ensure the recipient is periodically reminded over the next 20 minutes to respond. Simply click on the exclamation mark (!) > Urgent from within any chat.
- You can add your own tabs in any channel. This enables the use of other apps. The plus sign on the right of all channel tabs lets you see a list of apps that you can add.
- The "Files" tab enables the quick sharing of files with people on your team. You can upload them to SharePoint for collaboration instead of sharing links or emailing.
- The "Blur Background" option for video calls enables your background to be blurred, perfect when you're calling from home and wish to ensure privacy. Just flip it to "on" before making a call. Other background options are also available.
Learn about how to optimize performance in Microsoft Teams with these four tips. Also, learn more about the benefits and challenges of video conferencing.