WebRTC (Web Real-Time Communications)
What is WebRTC (Web Real-Time Communications)?
WebRTC (Web Real-Time Communications) is an open source project that enables real-time voice, text and video communications capabilities between web browsers and devices. WebRTC provides software developers with application programming interfaces (APIs) written in JavaScript.
Developers use these APIs to create peer-to-peer (P2P) communications between internet web browsers and mobile applications without worrying about compatibility and support for audio-, video- or text-based content.
With WebRTC, data transfer occurs in real time without the need for custom interfaces, extra plugins or special software for browser integration. WebRTC enables real-time audio and video communication simply by opening a webpage.
How does WebRTC work?
WebRTC uses JavaScript, APIs and Hypertext Markup Language to embed communications technologies within web browsers. It is designed to make audio, video and data communication between browsers user-friendly and easy to implement. WebRTC works with most major web browsers.
WebRTC APIs perform several key functions, including accessing and recording video-, audio- and text-based data from devices to initiating, monitoring and ending P2P connections between devices via browsers and facilitating bidirectional data transfer over multiple data channels.
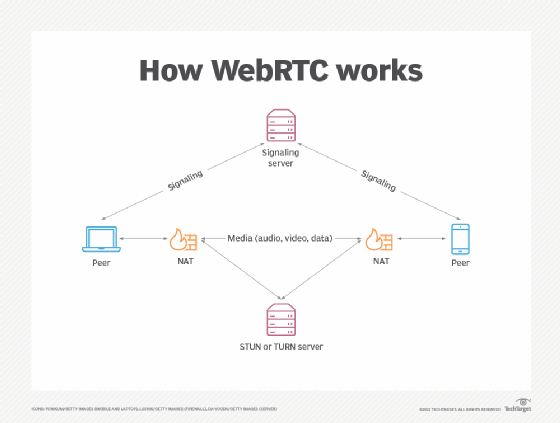
In most cases, WebRTC connects users by transferring real-time audio, video and data from device to device using P2P communications. In situations where users are on different Internet Protocol (IP) networks that have Network Address Translation (NAT) firewalls that prevent RTC, WebRTC can be used in conjunction with Session Traversal Utilities for NAT (STUN) servers. This enables a given IP address to be translated into a public internet address so peer connections can be established.
But there are also networks that are so restrictive that even a STUN server cannot be used to translate IP addresses. In these cases, WebRTC is used with a Traversal Using Relays around NAT (TURN) server, which relays traffic between users, enabling them to connect. The Interactive Connectivity Establishment protocol is used to find the best connection.
Before audio and video files are sent, they must be compressed due to their large size. Also, media that is received over a peer connection must be decompressed. WebRTC uses a codec process to do this.
What is WebRTC used for?
The goal of WebRTC is to facilitate real-time P2P communications over the internet. There are several use cases for WebRTC, including the following:
- WebRTC is used for video chats and meetings on video calling platforms, such as Zoom, Microsoft Teams, Slack or Google Meet.
- Industries, including healthcare, surveillance and monitoring, and internet of things, use WebRTC. For example, WebRTC use in Telehealth enables doctors to conduct virtual office visits with a patient over a web browser.
- In the field of home and business security and surveillance, WebRTC is used as a connecting agent between browsers and security cameras.
- WebRTC is heavily used for real-time media.
- WebRTC provides the underlying connection between instructors and students for online education.
What are the pros and cons of WebRTC?
WebRTC presents opportunities and challenges to organizations.
The advantages of WebRTC include the following:
- eliminates much of the in-house manual integration work required of IT;
- can adjust communication quality, bandwidth and traffic flow whenever network conditions change;
- is supported by most major web browsers, including Google Chrome for desktop and Android, Mozilla Firefox for desktop and Android, and Safari;
- works on any operating system as long as the browser supports WebRTC;
- does not require third-party components or plugins; and
- is free as open source software.
Disadvantages of WebRTC include the following:
- Each user must establish a P2P browser connection, making bandwidth an issue.
- Maintenance costs can be high because WebRTC requires powerful servers.
- Security and privacy standards are still unclear, leaving it up to IT departments to ensure that corporate security and privacy standards can be met.
- There are no definitive quality of service standards, which means that quality of video or audio over the internet may be inconsistent.
Is WebRTC secure?
Every WebRTC software component is encrypted, and every WebRTC API requires secure origins via Hypertext Transfer Protocol Secure (HTTPS) or localhost. Nevertheless, there are still open security questions that developers using WebRTC must consider. Signaling processing methods, or the methods used to exchange metadata, are not specified for WebRTC signaling. This means that developers must decide which security protocols to use and ensure that the protocols they select can be maintained with WebRTC.